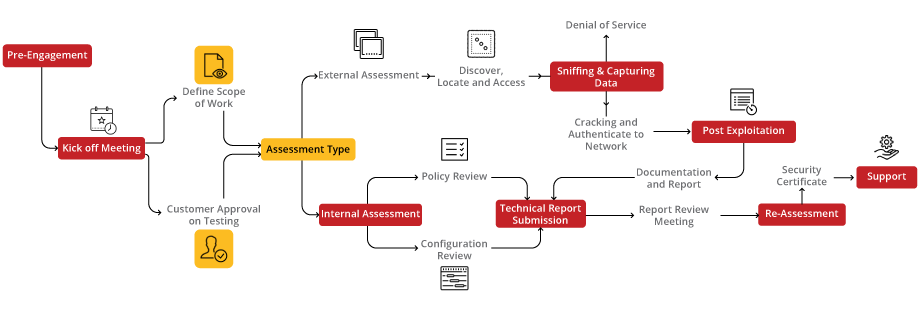
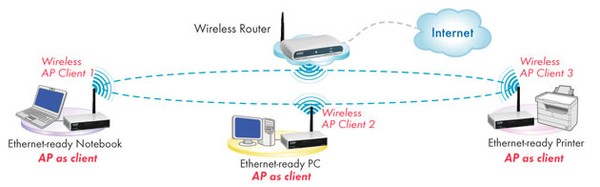
![PDF] Wireless Penetration Testing Method To Analyze WPA2-PSK System Security And Captive Portal | Semantic Scholar PDF] Wireless Penetration Testing Method To Analyze WPA2-PSK System Security And Captive Portal | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/e9023b8db564b7ec5d24322e3aad9e7ee92cafcf/2-Figure1-1.png)
PDF] Wireless Penetration Testing Method To Analyze WPA2-PSK System Security And Captive Portal | Semantic Scholar

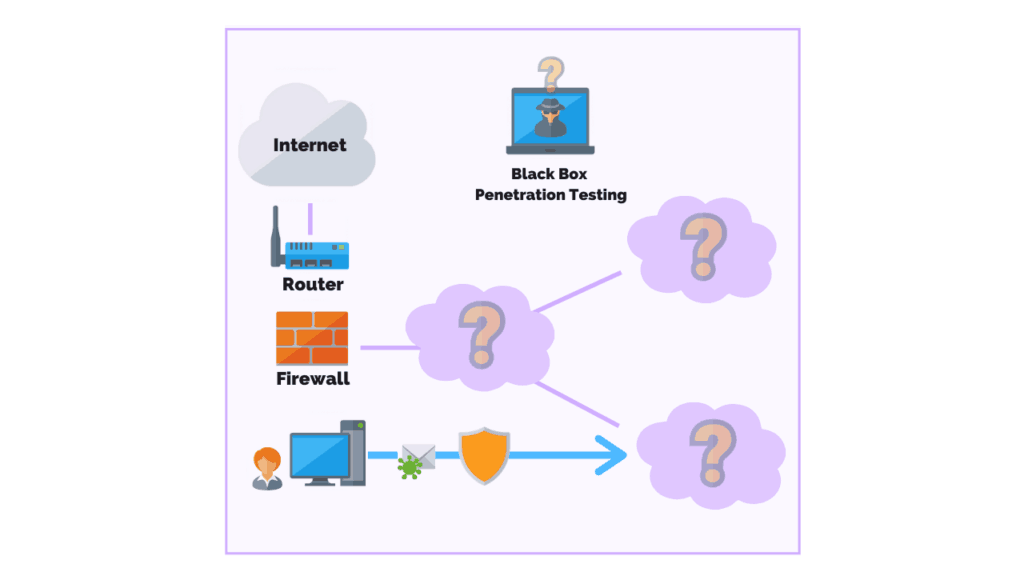
Kali Linux Wireless Penetration Testing: Beginner's Guide: Learn to penetrate Wi-Fi and wireless networks to secure your system from vulnerabilities: Ramachandran, Vivek, Buchanan, Cameron: 9781783280414: Amazon.com: Books